Data security and governance
Rational BI is built with a security-first approach to enterprise data governance and defense-in-depth security practices.
Architected for data security and defense in depth
Rational BI has implemented a combination of best-in-class security, privacy and compliance controls that address data protection risks through the entire data lifecycle.
Cloud security architecture
Rational BI is hosted on a proven public cloud (Amazon AWS), which means that as a Rational BI customer, you'll inherit the robust standards of cloud security maintained by AWS, which Rational BI builds on top of for its own security best practices. Rational BI also uses industry best practices to develop and test the Rational BI product, ensuring that code quality meets our standards before becoming part of a Rational BI release.
For more information about our security practices, see our listing in the Cloud Security Alliance Star registry.

Security practices
Rational BI uses AES 256 bit encryption to secure data in transit, and cached data is stored encrypted at rest. Plus, TLS 1.2 is used to encrypt network traffic between users' browsers and the Rational BI platform. SAML 2.0 SSO is supported for Rational BI Enterprise customers. All customers can enable 2FA on their accounts. If SSO is used, Rational BI will inherit the login security settings in the user's IdP or Google account.
In some cases, enterprise policies prevent data from leaving the corporate network, even when sent through a secured data connection. In those cases, Rational BI supports querying on-premise data directly, with no data ever traversing the network to the Rational BI cloud. A fully configurable data access layer allows the flexibility to set up data sourcing policies for each data source to ensure that data is governed at each step in the reporting pipeline.
Rational BI adheres to the principles of least privilege and policy-based permissions both for customer accounts and our internal organization. We always employ multi-factor authentication for access to internal systems.
Network security & system monitoring
Rational BI segments its systems into separate networks compliant with appropriate guardrails within AWS ControlTower. Network access to Rational BI's production environment from open, public networks is restricted, with only the load balancers accessible from the Internet. We keep extensive audit logs connected to our SIEM solution for centralized logging, auditing and threat detection.
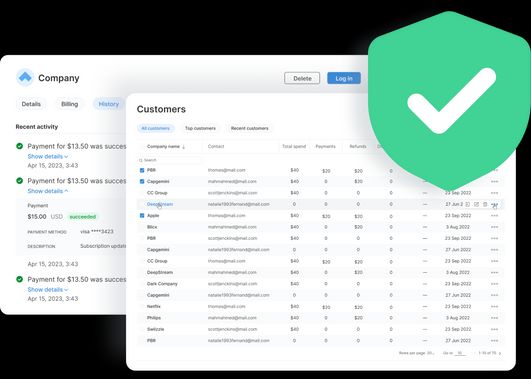
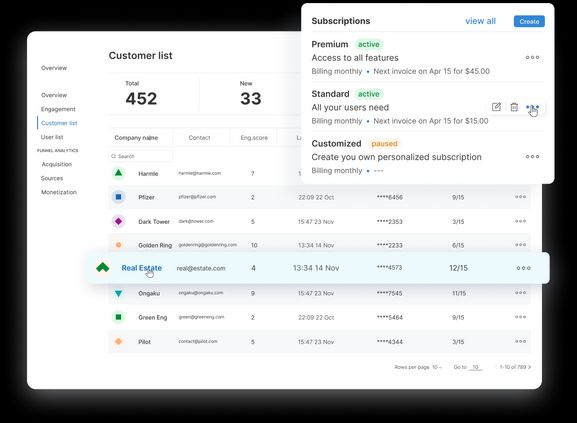
Policy-based security model
Rational BI secures data with granular policy-based access control lists. Assign specific access rights either on group or user role levels. Use our default policies, ranging from viewer to power user, or add your customized policies.
Flexible user management
You have several options for integrating your existing users with Rational BI.
- Integrate Rational BI with Single Sign-On through SAML available to any SAML IdP.
- Use the API to issue access tokens that can be exchanged for short-lived Rational BI sessions.
- Use the API to synchronize users between systems.
- Configure Rational BI to call out through a webhook to query your system for live authentication information for custom implementations.
Disaster recovery & incident response
Rational BI utilizes AWS services to distribute production operations across separate availability zones. These distributed zones protect Rational BI's service from loss of connectivity, power infrastructure, and other common location-specific failures.
Data privacy
Rational BI's production environment is hosted on an AWS platform. Data can also be found in Rational BI backups, stored in AWS, S3 and Glacier.
Rational BI follows GDPR and CCPA guidelines to ensure data protection obligations to our customers. This includes only collecting, processing, and storing customer data in compliance with these obligations and providing you the right to access or delete it at any time. Rational BI also requires our data processing vendors to certify the use of customer data for no other purpose than the provision of services. We provide controls for deleting customer data when it is no longer needed for a legitimate business purpose.
Responsible Disclosure
If you believe you have discovered a problem or have any questions, please get in touch with us at security@rationalbi.com. Where possible, encrypt your email message using our public GPG key. (Fingerprint: 'B168 E626 D615 64E7 B357 F8B0 2CBD 2FAA 8080 9564')
Reporting Issues
To those individuals who follow our "Responsible Disclosure Policy," Rational BI commits to: Promptly acknowledge receipt of your vulnerability report Provide an estimated timetable for resolution of the vulnerability Notify you when the vulnerability is fixed Acknowledge your help and reward you for identifying the issue!
Blog
Read more →Turn your data into a revenue stream
Talk to us and learn how to turn your data into a subscription product